My Cyberdeck
TL;DR — My custom "computer" from a future that never was...
6 minutes
Posted: August 14, 2043
After spending the last few months collecting parts, I was finally able to piece together my new cyberdeck over this weekend, and I must say, I’m pretty pleased with the result. Most of the equipment I used is vintage (or, as some might call it, “outdated junk”), but it supports a number of different data formats and interaction modes, making it handy for a variety of uses.
The main unit is a Tec<Net Walkabout T4 portable terminal with an upgraded Sino-Logic 16 processor (replacing the original 12-core version). Additionally, I ripped out the old port interface module and replaced it with a new one from OdaCom that supports USB-6X, SimStims, about 12 different kinds of ISO-chips, TriD, and even HDMI-Classic (so I can plug it in to any of the old displays in my workshop). Unfortunately, the original display on the Walkabout was cracked, and since I wanted it to be portable, I had to replace the screen with a 20-year-old (pre-merger) Samsung Android that I hardwired into the display adapter. I mean, it’s only a Super AMOLED screen (so, only 2D content), but it’ll work for now (maybe I’ll have better luck the next time I go to the E-Cyc center).

Software-wise, I decided to stick with what I know, and that was EncomOS. I’ve been using that particular flavor of GNU/Linux since the Meta / Microsoft merger and the Zuckerberg Affair, and since I already had root access to the Walkabout, it was an easy update to make.
As I said, I’m very happy with the end result, but I honestly I don’t know if I’m finished yet. I was going to put a GPL Stealth Module in it, But I may wait until I actually need it (especially since the crypto-cops tend to hassle anyone carrying one anymore). Likewise, I could replace the display with a short-throw holoview, or even plug a set of Thompson Eye-Phones in to the Hub, but I’m comfortable enough in both shell and 2D GUI to get by without VR for most activities (plus, since the optical data cord is hot swappable, I can always plug in the Eye-Phones in when I want the full XR experience).
I’ve embedded some more images below, in case you want to see more. As I said, I’m quite happy with the finished product, and have already started thinking about what to add to the next version.
I’ll keep sharing updates on any future improvements I make to it.

OK, it obviously isn’t 2043 (yet), but the images above are real, and I really did “build” a cyberdeck (several years ago, in fact).
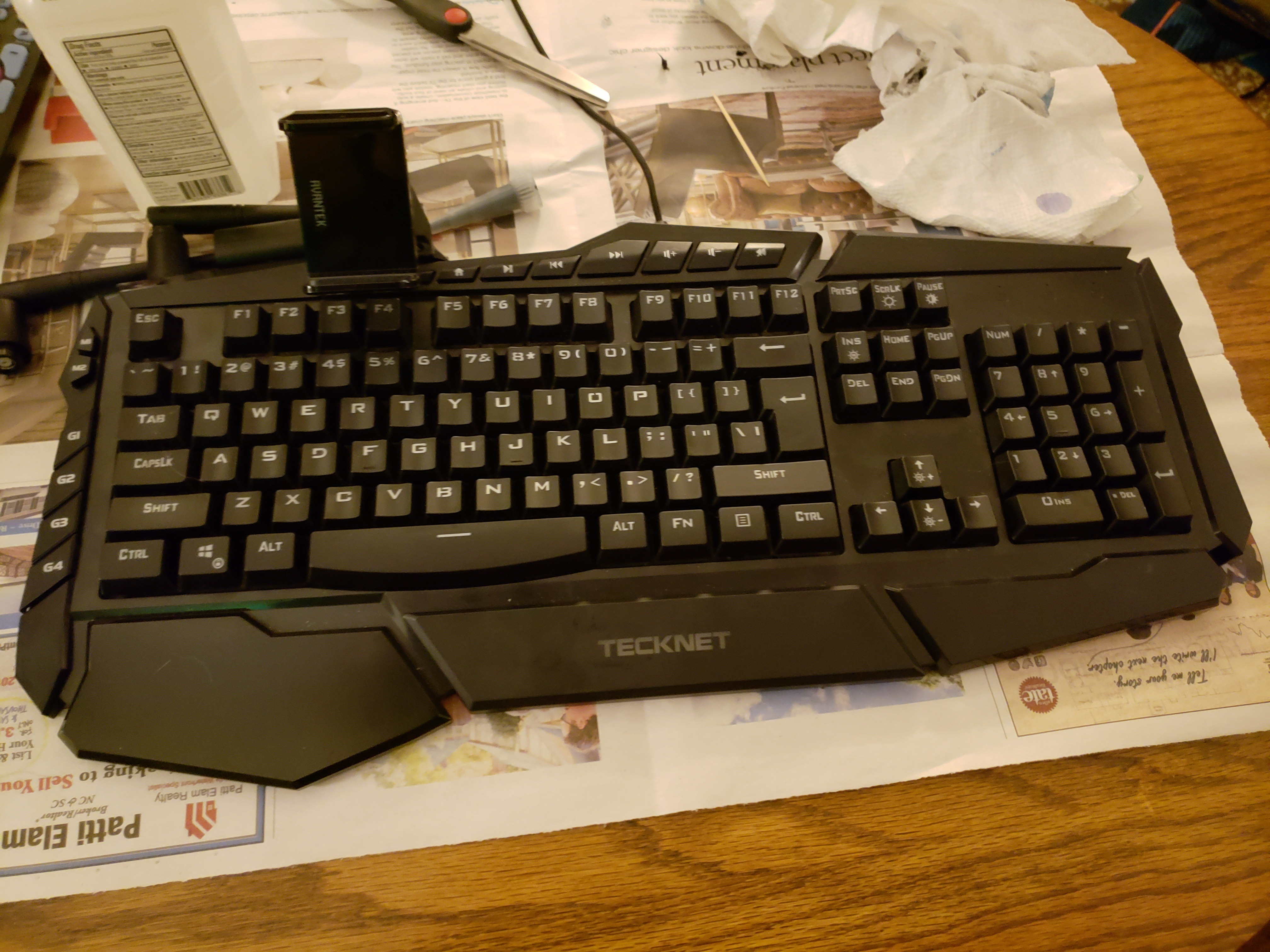
At present, the “brains” of the device is a Samsung Galaxy s23 smartphone, connected via USB-C to a hub. The hub, in turn, is connected to a TeckNet Heavy Duty back-lit keyboard via a USB cable and is physically attached to it via silicon and Sugru. A 2600 mAh power bank that I picked up cheap a few years ago is also glued to the keyboard, and a metal brace is attached to both the keyboard and power bank, giving it some stability, as well as a place for the phone mount to attach (via magnets).


The hub has 2 USB-3 ports (one of which is dedicated to the keyboard, but that’s OK), a TF card slot, an SD card slot, a USB-C charging port, and an HDMI port. Overall, the device is lighter than a notebook but more tactile than a glass screen, and sits very easily on my lap.

I had originally intended to attach both the USB hub and phone mount to the keyboard via some kind of tab-and-slot sliding mechanism (not unlike how Joy-Cons attach to the Nintendo Switch), but I couldn’t find the hardware I would need to implement it. Still, if I do another one, I’d like to explore that as an option, making the whole device more modular (being able to swap out different USB hubs for different needs, and maybe alternate mounts, so I could use a tablet instead of my phone).
I built it over the past couple of years, and actually went through several updates along the way (improving the hubs and phone holster).

I’m sharing it now because I’m entering the Hackaday Cyberdeck contest (my entry). This post is mostly the same info that’s over there.
Of course, it’s not perfect - it’s not as durable as I’d like it to be, and it’s not exactly easy to carry. My hope had been to mount the whole thing to either some kind of metal frame or plate (a la a hiking backpack, but smaller), providing some much need structural support (and stable grips to hold on to), but I could never find what I was looking for. Plus, I built it before my current obsession with mechanical keyboards, so while the keyboard is nice, it doesn’t have quite the desired click.
But, all-in-all, it was a fun project to put together, and it’s come in handy more thana few times (when I was between machines, or waiting on repairs).
How well does it work?
Overall, I think it works well. Although the small screen limits some of its functionality, the relative simplicity of a phone-based system does lend itself to certain tasks, like journaling and shell-based interfaces (like MOSH), two things I like to use it for. A previous iteration of this design was powered by an S9 which even ran a web server (a virtual machine running nginx and nodeJS), and the keyboard was useful for direct access to the shell.
At the end of the day, the phone is a very powerful device in-and-of-itself, and the added functionality that comes fromt he hubs (whether for extra memory, peripherals, or even an external monitor
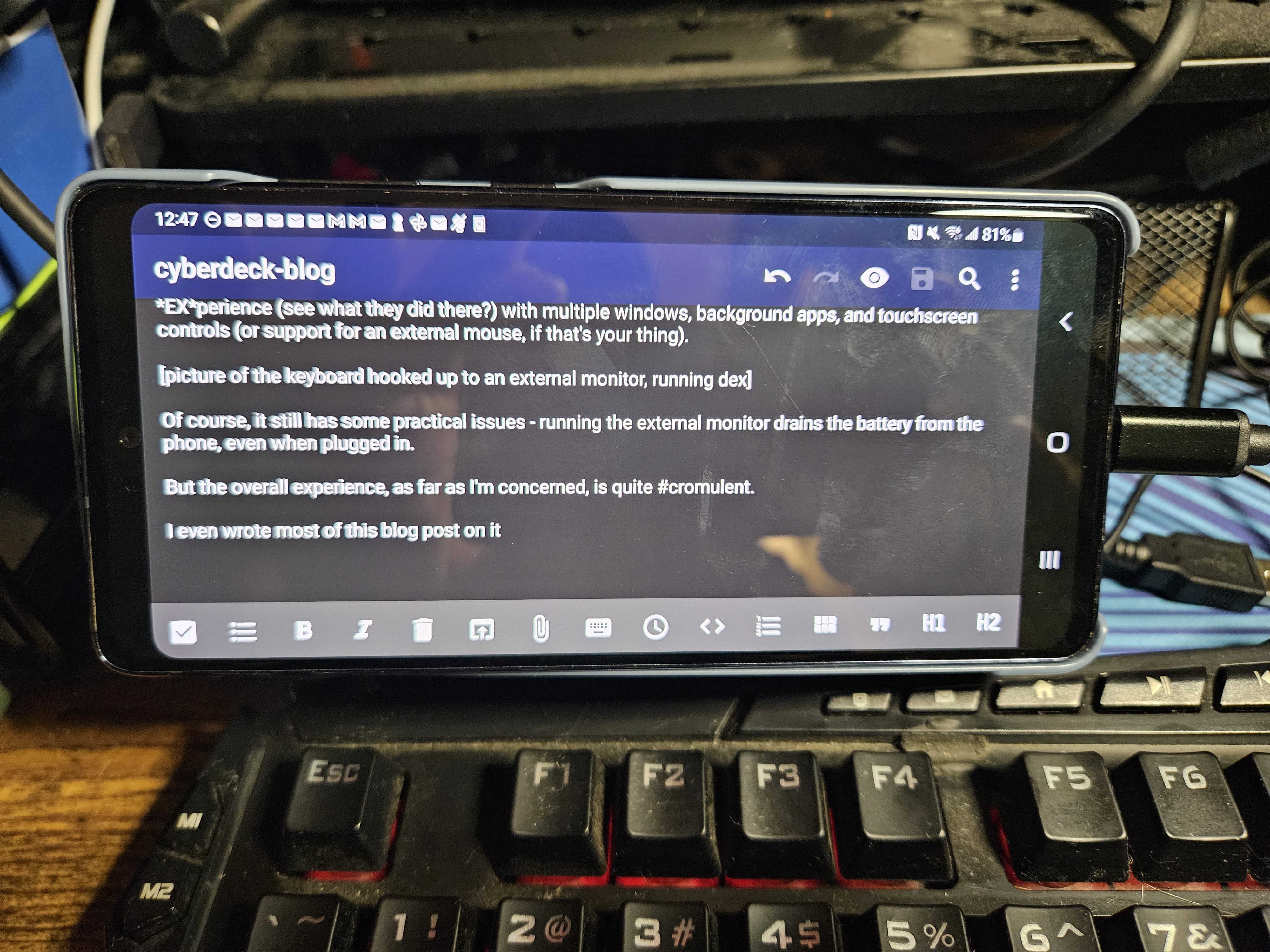
Plus, because it’s a Samsung phone, plugging it into a monitor activates DEX mode, a Desktop-like EXperience (see what they did there?) with multiple windows, background apps, and touchscreen controls (or support for an external mouse, if that’s your thing).
[picture of the keyboard hooked up to an external monitor, running dex]

Of course, it still has some practical issues - running the external monitor drains the battery from the phone, even when plugged in.
But the overall experience, as far as I’m concerned, is quite #cromulent .
I even wrote most of this post on it.

Does it support VR?
It does, or it did, sort of, but not for long.
Given that the phone is the brain of the “device”, any USB-C compatible phone can be plugged into it. The previous brains for the device were a Samsung Galaxy S9 and S10, each of which could plug into a Samsung Gear VR.
Unfortunately, Samsung discontinued it, so it doesn’t work with the s20 (the current brain) or later. I keep hoping that these devices will somehow get “opened up” with later non-standard firmwares and enable something like the failed Project DayDream to live up to it’s full potential.
Conclusion
In the end, I haven’t used it much - it’s too unwieldy to take anywhere, and if I’m honest, I don’t do alot of mobile computing where it would be useful. I had planned to address the first issue by mounting the device on a metal frame, and maybe I will if I ever work on a v2, but for now, it remains sans handle or reinforcing structure.
And so it mostly sits, collecting dust… just a souvenir from a future that never was.